Endpoint enrichment - Crowdstrike
Browse: 🏠 · Solutions · Connectors · Methods · Tables · Content · Parsers · ASIM Parsers · ASIM Products · 📊
When a new Microsoft Sentinel incident is created, this playbook gets triggered and performs below actions:
| Attribute | Value |
|---|---|
| Type | Playbook |
| Solution | CrowdStrike Falcon Endpoint Protection |
| Source | View on GitHub |
Additional Documentation
📄 Source: CrowdStrike_Enrichment_GetDeviceInformation/readme.md
Crowdstrike_Enrichment_GetDeviceInformation
## Summary When a new Microsoft Sentinel incident is created, this playbook gets triggered and performs below actions: 1. Fetches the device information from Crowdstrike 2. Enrich the incident with device information from Crowdstrike
Prerequisites
- Azure Key vault is required for storing the Crowdstrike ClientID and Secrets, create key vault if not exists learn how
- Add Crowdstrike Client ID and Client Secret in Key vault secrets and capture the keys which are required during the template deployment
- CrowdStrike_Base playbook needs to be deployed prior to the deployment of this playbook under the same subscription and under the same resource group.
- CrowdStrike_Base playbook needs to be added in the access policy of the Key Vault learn how
Deployment instructions
- Deploy the playbook by clicking on "Deploy to Azure" button. This will take you to deploying an ARM Template wizard.
- Fill in the required parameters:
- Playbook_Name: Enter the playbook name here (Ex:Crowdstrike_ContainHost)
- CrowdStrike_Base_Playbook_Name : Enter the base playbook name here (Ex:CrowdStrike_Base)
Post-Deployment instructions
a. Authorize connections
Once deployment is complete, you will need to authorize connections. 1. Click the Microsoft Sentinel connection resource 2. Click edit API connection 3. Click Authorize 4. Sign in 5. Click Save
b. Configurations in Sentinel
- In Microsoft sentinel analytical rules should be configured to trigger an incident with risky device
- Configure the automation rules to trigger this playbook
Playbook steps explained
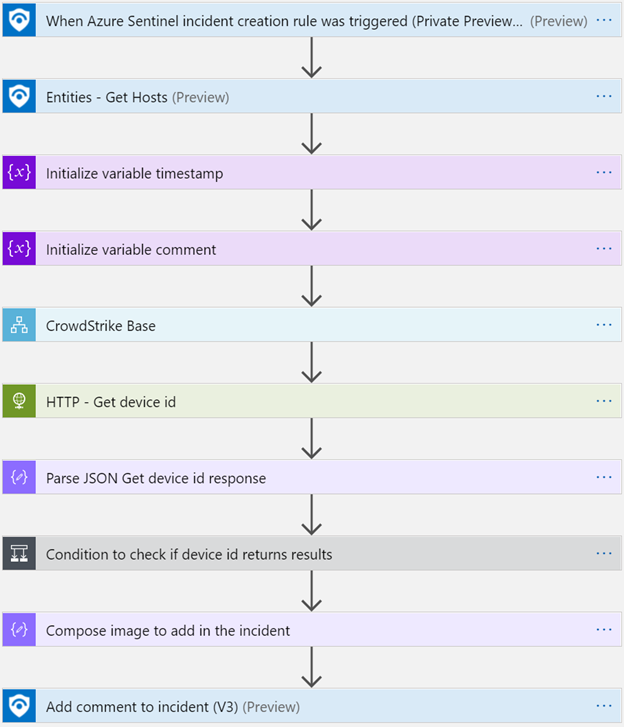
When Microsoft Sentinel incident creation rule is triggered
Microsoft Sentinel incident is created. The playbook receives the incident as the input.
Entities - Get Hosts
Get the list of risky devices as entities from the Incident
Initialize_variable_comment
Initialize a string variable to store comments to update in the incident
Initialize variable timestamp
Initialize timestamp variable to hold the timestamp for the past 3 days
CrowdStrike Base
Call the base logic App to get access token and Falcon Host URL
HTTP-Get device id
This gets the device id from crowdstrike by filtering on hostname
Parse JSON Get device id response
This prepares Json message for the device id response
### Condition to check if device is present in crowdstrike
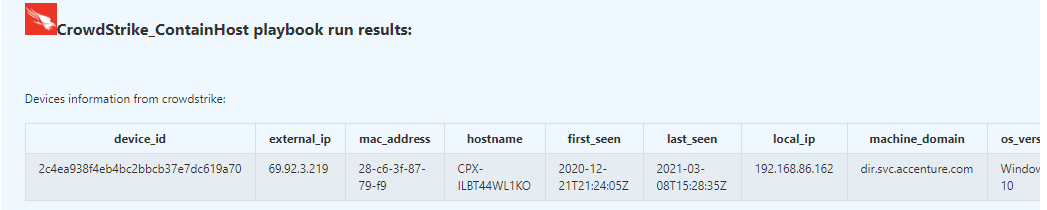
- If device is present, get the device information from crowdstrike API and prepares HTML table with required information
- Set the timestamp for past 3 days and search for detections on the host and get the detection information
- check if detection information is present create HTML table for detection information
### Compose image to add in the incident This action will compose the Crowdstrike image to add to the incident comments
Add a comment to the incident with the information
This action will enrich the incident with the constructed HTML table with device information
Browse: 🏠 · Solutions · Connectors · Methods · Tables · Content · Parsers · ASIM Parsers · ASIM Products · 📊
↑ Back to Playbooks · Back to CrowdStrike Falcon Endpoint Protection